Using Aerospike Cloud with AWS PrivateLink
AWS PrivateLink is the secure, private, connection between virtual private clouds (VPCs), supported AWS services, and Aerospike Cloud. AWS PrivateLink shields your traffic from the public internet. Interface VPC endpoints, which are also powered by PrivateLink, securely connect your client applications with Aerospike Cloud.
Prerequisites
- A running Aerospike Cloud instance.
- A client application running on AWS with an associated VPC and subnet.
Procedure
In the Aerospike Cloud console, navigate to the Configurations tab in your desired database.
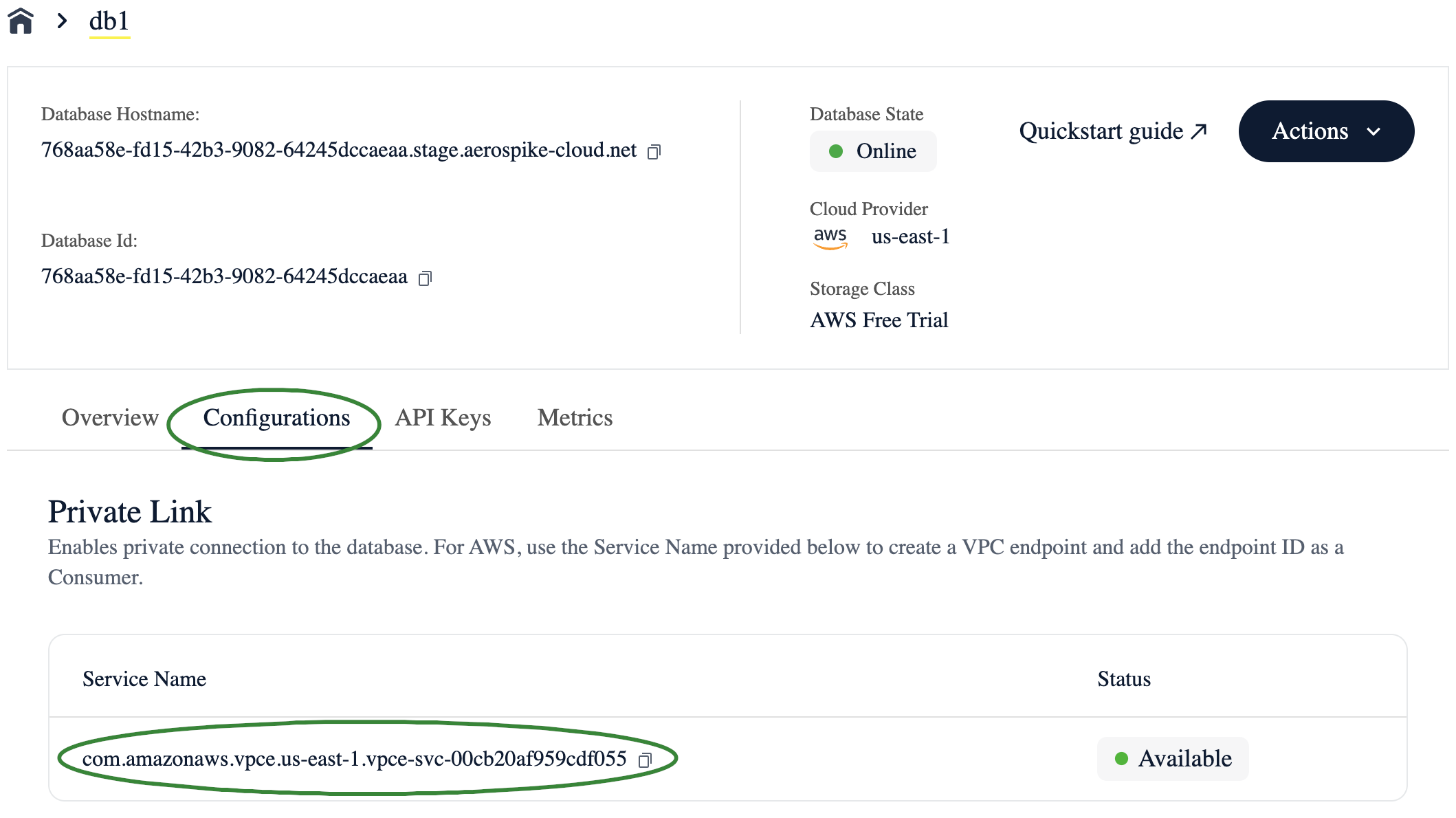
Confirm that there is a Service Name listed in the PrivateLink section of the page. This is an AWS VPC endpoint service that your database can use for PrivateLink connections.
Create a connection from your client application to your Cloud database.
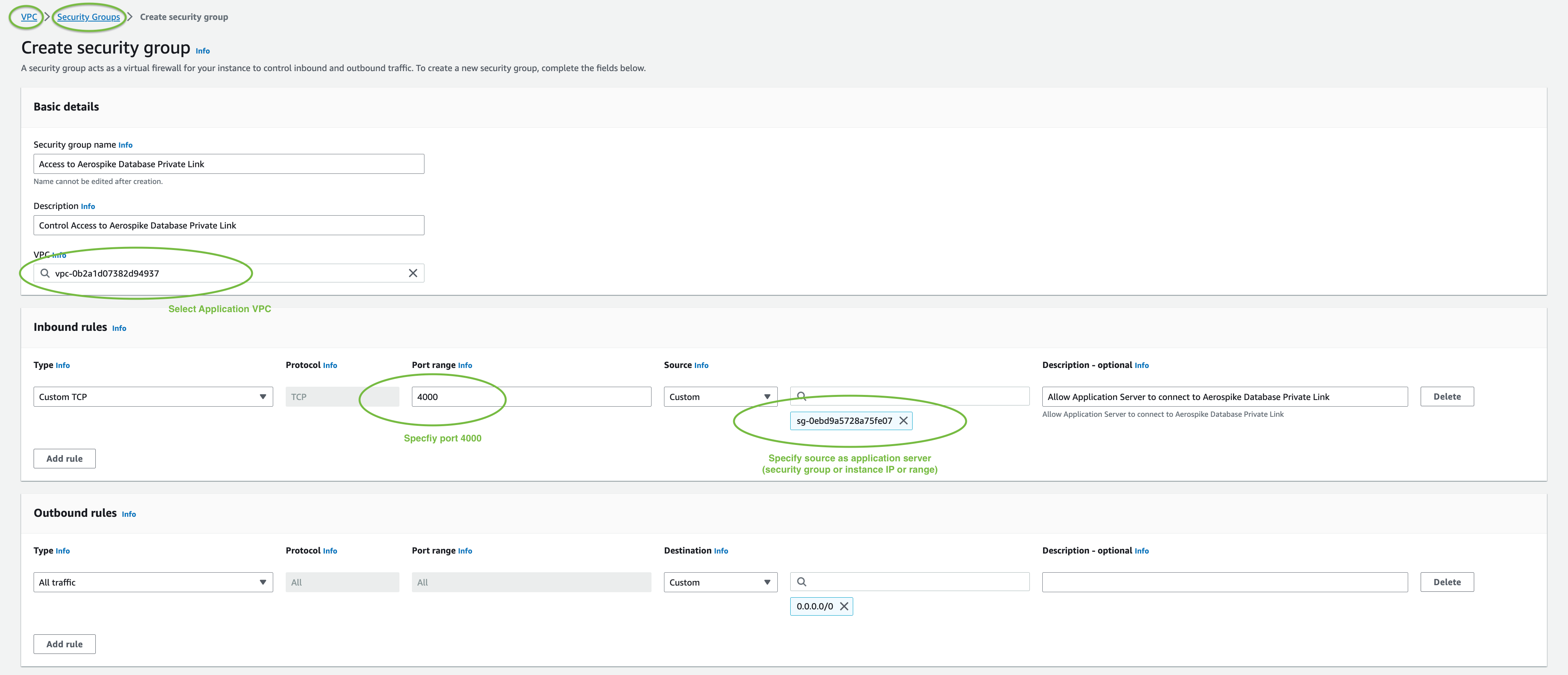
In the AWS console, create a security group in the application VPC to allow traffic from the application server to your VPC endpoint service.
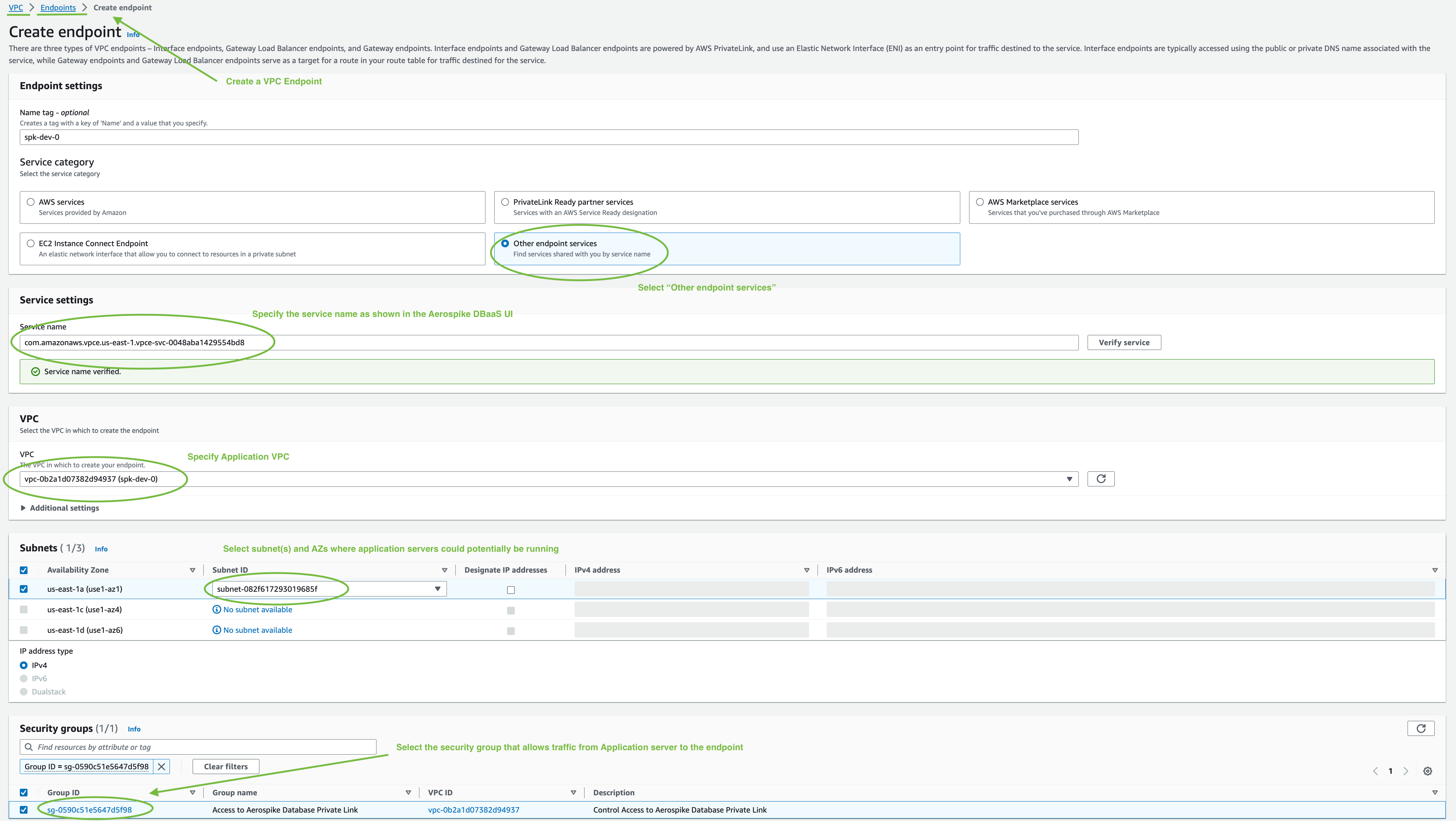
Create a VPC endpoint in your application's VPC to connect to the Aerospike Cloud PrivateLink endpoint service.
After you create the VPC endpoint, it is in a
Pending acceptancestate.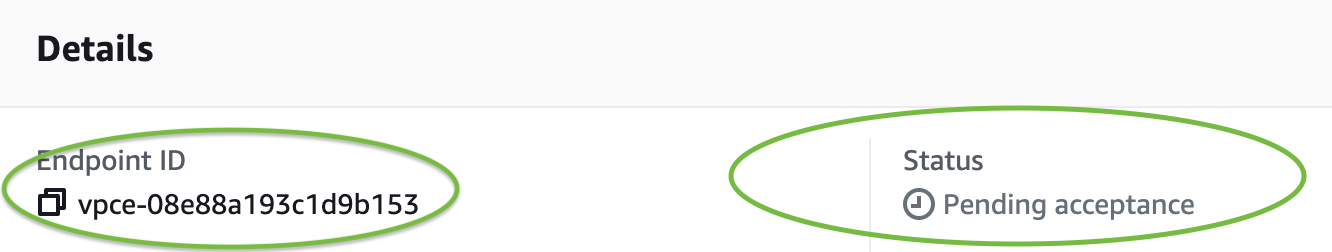
Copy the VPC endpoint ID for use in the next step.
In the Aerospike Cloud console, click Create Consumer to create a PrivateLink Consumer with the VPC endpoint ID.
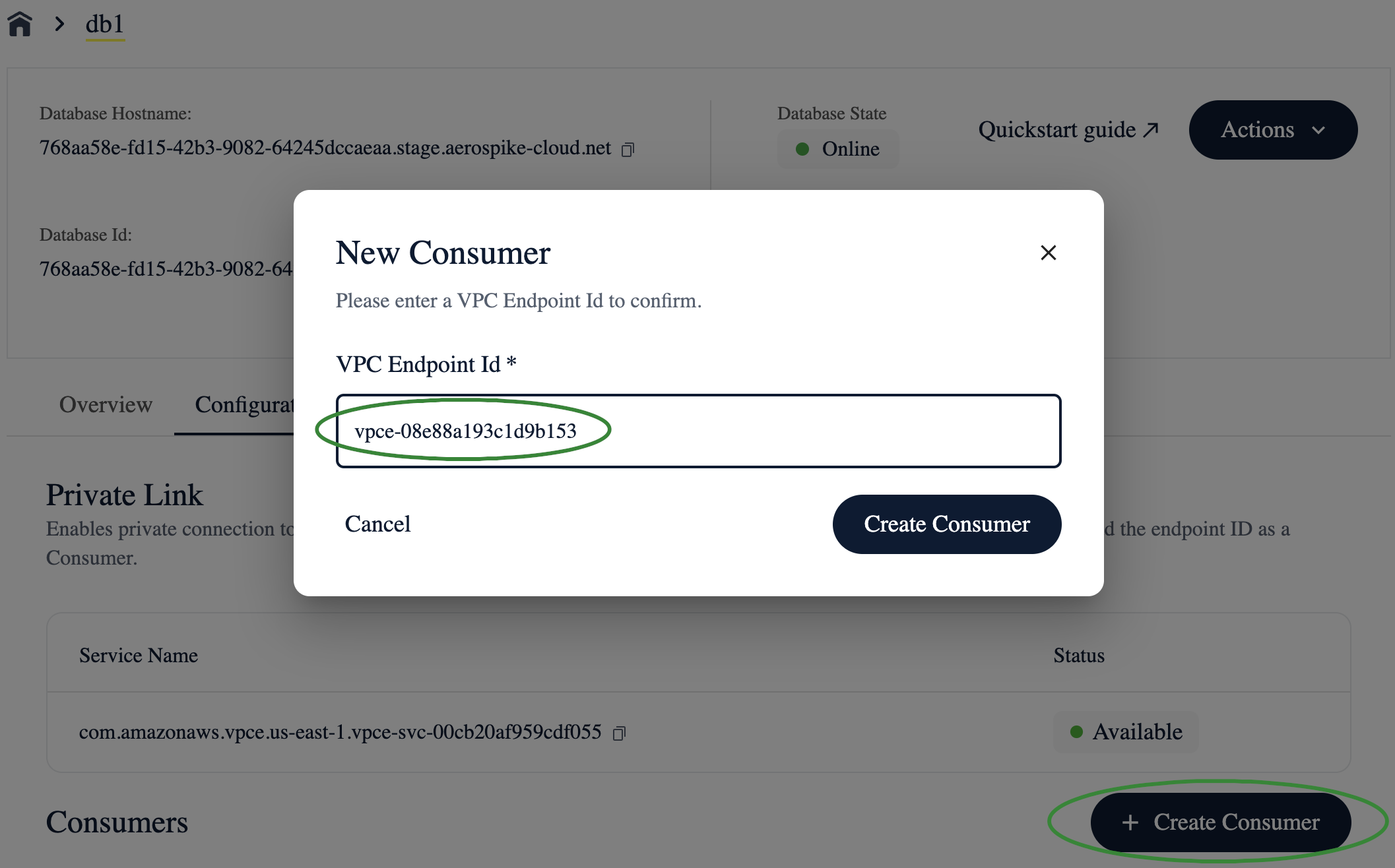
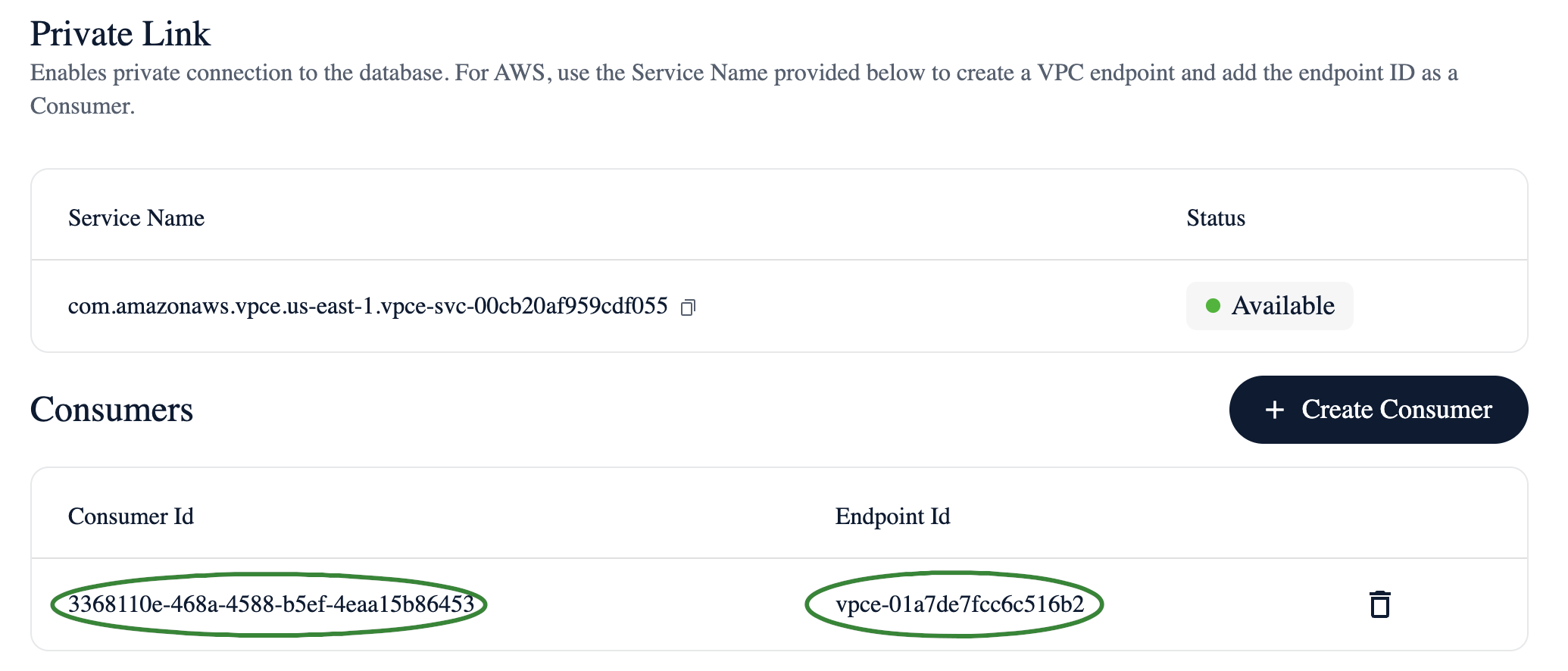
After you click Create Consumer, it takes a few seconds for the connection to be accepted. When it's ready, a new entry appears in the Consumers section of the Configurations page.
In the AWS console, the VPC endpoint status updates from
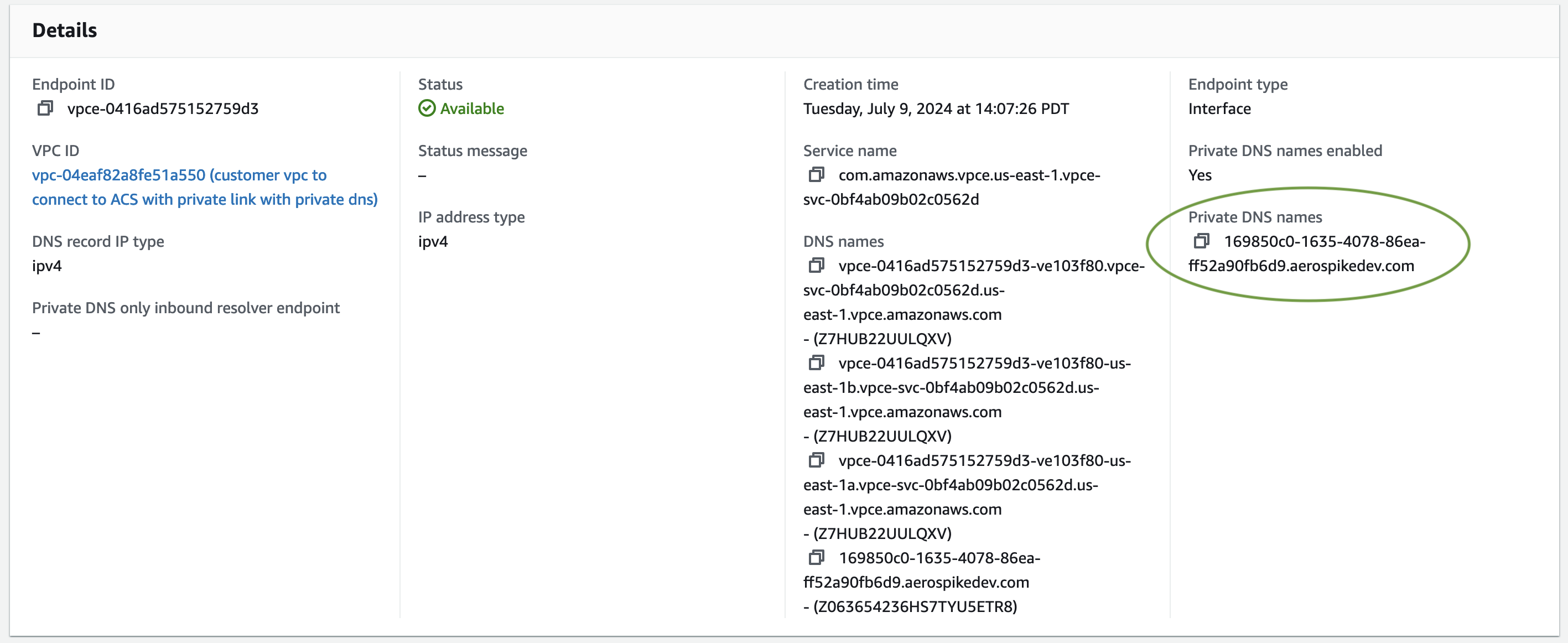
PendingtoAvailable.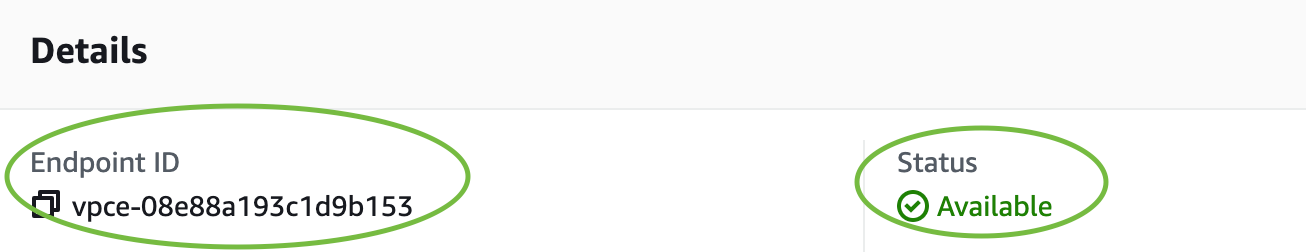
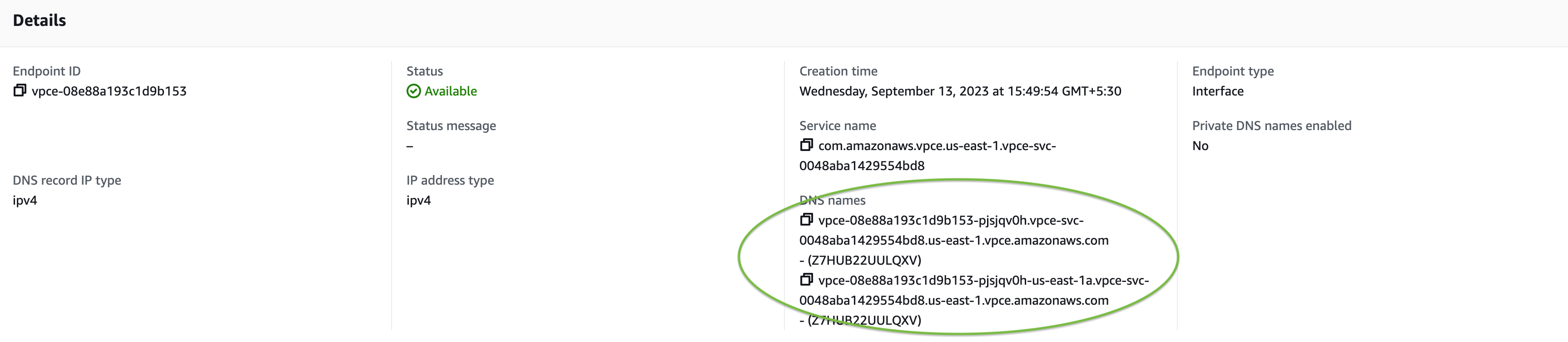
Once the status shows
Available, your client application can connect to your Cloud database through PrivateLink. In your application's connection code, you can specify any of the following as seed hostnames:- VPC endpoint DNS names.
- VPC endpoint IP address.
- DNS names created in either private or public hosted zones that resolve to either a VPC endpoint DNS name or its IP address.
Enable Private DNS.
After the endpoint is accepted, manually edit the endpoint and enable Private DNS.
HTTPS is enforced over the PrivateLink connections to the database.
Set the ServerName property in your client TLS configuration to
the original database host name. This is required for the host name verification.
Your database host name is of the form <DATABASE_ID>.asdb.io. You can find your
<DATABASE_ID> in the top panel of the Cloud console.
Private DNS cannot be enabled during the creation of the VPC endpoint. It must be enabled after the endpoint is created and accepted. Verify that you use the Private DNS name in your connection configuration once it is enabled.
Code examples
Replace all placeholder and example values with the correct values for your application configuration.
- Go
clientPolicy := aerospike.NewClientPolicy()
clientPolicy.User = "<API_KEY_ID>"
clientPolicy.Password = "<API_KEY_SECRET>"
clientPolicy.TlsConfig = &tls.Config{
ServerName: "6b45cfdc-7dec-44de-853c-9baed45a02a6.asdb.io",
}
host := aerospike.NewHost("vpce-08e88a193c1d9b153-pjsjqv0h.vpce-svc-0048aba1429554bd8.us-east-1.vpce.amazonaws.com", 4000) // Use the VPC endpoint DNS name
client, err := aerospike.NewProxyClientWithPolicyAndHost(clientPolicy, host)
if err != nil {
// handle error
}
// Update the ServerName and host if Private DNS is enabled and accepted
/*
clientPolicy.TlsConfig.ServerName = "169850c0-1635-4078-86ea-ff52a90fb6d9.aerospikedev.com"
host = aerospike.NewHost("169850c0-1635-4078-86ea-ff52a90fb6d9.aerospikedev.com", 4000) // Use the private DNS name
*/